MobSF/Mobile-Security-Framework-MobSF

Mobile Security Framework (MobSF) is an automated, all-in-one mobile application (Android/iOS/Windows) pen-testing, malware analysis and security assessment framework capable of performing static and dynamic analysis.
| repo name | MobSF/Mobile-Security-Framework-MobSF |
| repo link | https://github.com/MobSF/Mobile-Security-Framework-MobSF |
| homepage | https://opensecurity.in |
| language | Python |
| size (curr.) | 488482 kB |
| stars (curr.) | 5565 |
| created | 2015-01-31 |
| license | GNU General Public License v3.0 |
Mobile Security Framework (MobSF)
Version: v3.0 beta

Mobile Security Framework (MobSF) is an automated, all-in-one mobile application (Android/iOS/Windows) pen-testing, malware analysis and security assessment framework capable of performing static and dynamic analysis. MobSF support mobile app binaries (APK, IPA & APPX) along with zipped source code and provides REST APIs for seamless integration with your CI/CD or DevSecOps pipeline.The Dynamic Analyzer helps you to perform runtime security assessment and interactive instrumented testing.
Made with  in India
in India
MobSF is also bundled with Android Tamer and BlackArch
Support MobSF
Documentation
- Try MobSF Static Analyzer Online:

- Conference Presentations: Slides & Videos
- MobSF Online Course: OpSecX MAS
- What’s New: See Changelog
Collaborators
Ajin Abraham  | Dominik Schlecht
| Dominik Schlecht  | Magaofei
| Magaofei  | Matan Dobrushin
| Matan Dobrushin  | Vincent Nadal
| Vincent Nadal 
e-Learning Courses & Certifications
 Automated Mobile Application Security Assessment with MobSF -MAS
Automated Mobile Application Security Assessment with MobSF -MAS
 Android Security Tools Expert -ATX
Android Security Tools Expert -ATX
MobSF Support
- Free Support: For free limited support, questions and help, join our Slack channel
 mobsf.slack.com
mobsf.slack.com - Enterprise Support: For enterprise support, priority feature requests and live training, see MobSF Support Packages
Contribution, Feature Requests & Bugs
- Read CONTRIBUTING.md before opening bugs, feature requests and pull request.
- For Project updates and announcements, follow @ajinabraham or @OpenSecurity_IN.
- Github Issues are only for tracking bugs and feature requests. Do not post support or help queries there. We have a slack channel for that.
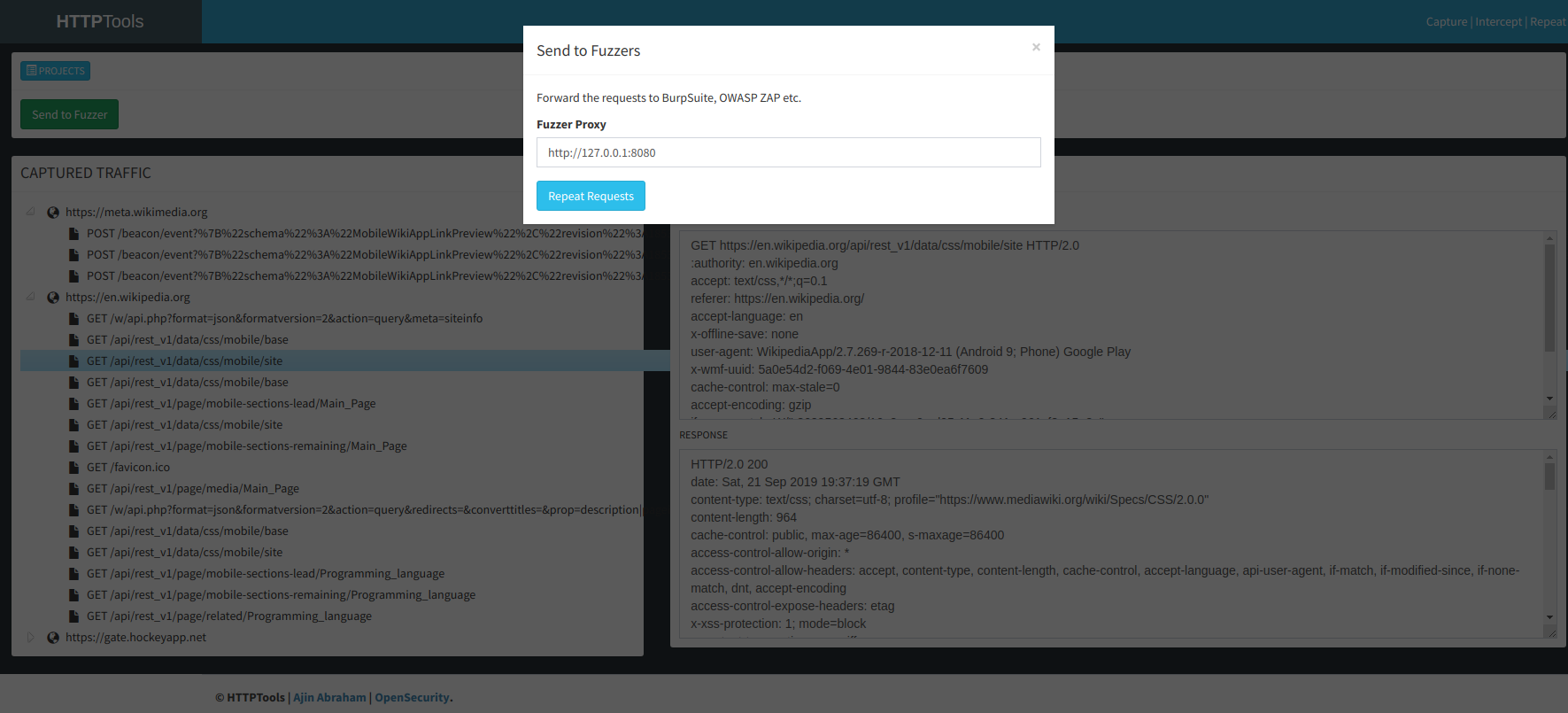
Screenshots
Static Analysis - Android



Static Analysis - iOS



Dynamic Analysis - Android APK



Web API Viewer
Honorable Contributors
- Amrutha VC - For the new MobSF logo
- Dominik Schlecht - For the awesome work on adding Windows Phone App Static Analysis to MobSF
- Esteban - Better Android Manifest Analysis and Static Analysis Improvement.
- Matan Dobrushin - For adding Android ARM Emulator support to MobSF - Special thanks goes for cuckoo-droid
- Shuxin - Android Binary Analysis
- Abhinav Saxena - (@xandfury) - For Travis CI and Logging integration
 Netguru (@karolpiateknet, @mtbrzeski) - For iOS Swift support, Rule contributions and SAST refactoring.
Netguru (@karolpiateknet, @mtbrzeski) - For iOS Swift support, Rule contributions and SAST refactoring.
Shoutouts
- Abhinav Sejpal (@Abhinav_Sejpal) - For poking me with bugs, feature requests, and UI & UX suggestions.
- Anant Srivastava (@anantshri) - For Activity Tester Idea
- Anto Joseph (@antojosep007) - For the help with SuperSU.
- Bharadwaj Machiraju (@tunnelshade_) - For writing pyWebProxy from scratch
- Rahul (@c0dist) - Kali Support
- MindMac - For writing Android Blue Pill
- Oscar Alfonso Diaz - (@OscarAkaElvis) - For Dockerfile contributions
- Thomas Abraham - For JS Hacks on UI.
- Tim Brown (@timb_machine) - For the iOS Binary Analysis Ruleset.